Intelligence Is the New Firewall: Why Static Defences Are Dead

Table of contents
Intelligence Is the New Firewall: Why Static Defences Are Dead
Executive Summary
- Telecom fraud controls were designed to detect suspicious signals and protect the infrastructure underlying the network, not expose threat actors and scam operations themselves.
- Modern scam campaigns operate as coordinated networks using telecom infrastructure.
- Traditional detection tools see traffic patterns but cannot interrogate the scam payload.
- Intelligence-led visibility reveals the campaign infrastructure behind scam traffic.
- Real deployments show improved precision, lower false positives, and scalable disruption.
- A live deployment with TPG Telecom demonstrates measurable improvements in both disruption outcomes and network accuracy.
The Telecom Network Has Become the Delivery Layer for Scams
Telecommunications infrastructure now sits at the centre of modern scam operations. Voice calls and SMS remain the primary delivery mechanisms because they scale globally, create a sense of legitimacy, and bypass many forms of digital platform security.
For threat actors, telecom networks provide reach, immediacy, and trust. For operators, this poses a unique problem. The network carries the communication that harms customers, yet the underlying operation often remains hidden within otherwise normal-looking traffic.
Scam campaigns frequently combine VoIP infrastructure, rotating numbers, distributed call centres, and mule networks to move funds. These operations can be launched rapidly and repeated across multiple markets with only minor adjustments to scripts or impersonation narratives.
From a telecom perspective, the technical signals generated by this activity often resemble ordinary communication behaviour.
Key implications for telecom networks:
- The network becomes the delivery layer for social engineering campaigns.
- Traffic carrying scams may appear technically legitimate.
- Detection frequently occurs only after large volumes of calls have already been attempted.
.png)
Strong Controls, but the Wrong Layer
Telecom operators have invested heavily in security infrastructure over the past decade. Modern networks deploy signalling firewalls, fraud management platforms, CLI spoofing detection, number reputation systems, anomaly detection engines, and rule-based filtering.
These systems play a critical role in protecting network infrastructure and detecting abnormal traffic patterns. They are effective at identifying signalling anomalies, suspicious routing behaviour, and known forms of abuse.
However, they operate at the signal layer of telecom activity. They analyse metadata such as call origin, routing behaviour, volumes, and number reputation.
Scam campaigns operate differently.
The deception does not occur in the signalling itself. It occurs inside the conversation between the scammer and the victim. As long as the call connects normally and signalling appears valid, traditional fraud controls may have little reason to intervene.
This creates a structural limitation.
Detection systems rely on signals that often appear only after a campaign has already begun to scale. Numbers accumulate reputation after they have been used. Anomalies emerge once traffic volumes increase. Blocking rules are updated in response to patterns that have already occurred.
Meanwhile, the underlying operation adapts. Infrastructure is replaced, numbers are rotated, and campaigns continue under new variations.
Operational limitations of signal-layer controls:
- Detection relies on anomalies or reputation signals that appear after activity has begun
- Blocking decisions must balance security with the risk of false positives
- Individual artefacts such as numbers or routes can be replaced quickly
The Detection Gap - You Cannot Disrupt What You Cannot See
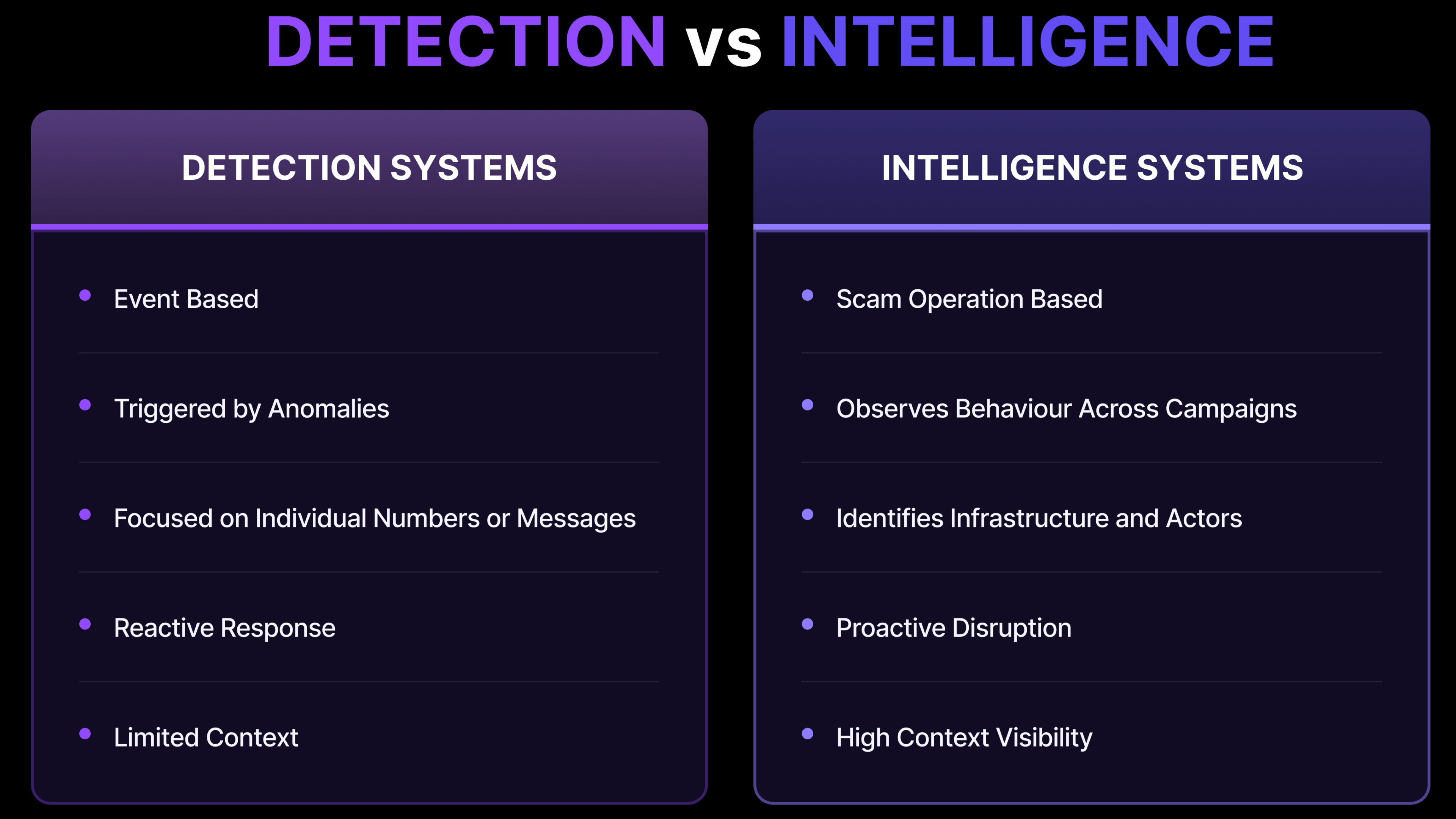
Understanding the persistence of scam activity requires separating telecom fraud prevention into two layers.
The first is the signal layer. This is where telecom networks naturally operate. Controls monitor signalling behaviour, call metadata, routing patterns, and reputation scores.
When something looks suspicious, actions are triggered such as blocking a number or restricting a route.
The second is the campaign layer. This is where the scam operation actually exists. Campaigns consist of operators, scripts, coordination between call centres, infrastructure reuse, and networks of mule accounts used to move stolen funds.
These elements rarely appear directly in telecom signalling data.
A scam call can look identical to a legitimate call at the signalling level. The social engineering payload exists entirely within the conversation itself.
This creates the detection gap.
Traditional telecom controls detect suspicious signals. Scam operations function as coordinated businesses that adapt quickly to avoid generating those signals.
Signals are removed, but the campaign continues.
Examples of campaign-layer behaviour invisible to signalling systems:
- Reuse of the same social engineering script across campaigns
- Organised operator shifts and campaign operating windows
- Infrastructure reuse across different scam operations
- Coordination with financial mule networks
If telecom operators want to move from reacting to scams toward disrupting them, the network must gain visibility into the campaigns themselves.
Because an operation that cannot be seen is almost impossible to dismantle.
.png)
.png)
How Scam Campaigns Actually Operate
Scam campaigns follow a repeatable operational lifecycle. The structure allows operators to scale their activity quickly while avoiding detection mechanisms that rely on static signals.
Most campaigns move through five stages.
Typical stages include:
Campaign preparation
- Scripts are written and impersonation narratives are developed. These frequently mimic trusted institutions such as banks, telecommunications providers, or government agencies.
Infrastructure acquisition
- Phone numbers, VoIP gateways, and routing pathways are obtained. Infrastructure may be distributed across multiple carriers or jurisdictions.
Traffic generation
- Calls or SMS messages are launched at scale, often during carefully selected time windows that maximise the likelihood of reaching victims.
Victim engagement
- Operators follow scripts designed to manipulate victims into transferring funds or revealing credentials.
Monetisation
- Stolen funds are moved through mule accounts and laundering channels.
Traditional telecom detection typically occurs during the traffic generation phase. By the time signals appear in network monitoring systems, the campaign may already have reached thousands of potential victims.
By that point, the campaign is already underway.
The Missing Layer: Intelligence
The signal layer shows what is moving through a telecom network. The intelligence layer explains why that activity is occurring.
Intelligence-led approaches focus on observing the behaviour of scam campaigns rather than relying solely on traffic anomalies.
This visibility makes it possible to identify patterns across campaigns. Scripts can be analysed, infrastructure reuse can be identified, and the operating windows of campaigns can be mapped.
When these patterns are visible, fraud prevention becomes more precise.
Benefits of campaign-level visibility:
- Detection improves because malicious behaviour can be distinguished with greater confidence.
- Disruption becomes more targeted because supporting infrastructure can be identified.
- Intelligence compounds over time as patterns of scam behaviour accumulate.
Instead of treating each suspicious call as an isolated event, the network begins to recognise the structure of the operation producing that activity.
.png)
Real World Outcomes: TPG Telecom
The impact of campaign-level intelligence becomes clearer when examined within a live telecom environment.
TPG Telecom deployed an intelligence-led approach that complemented its existing fraud detection infrastructure. Rather than relying only on blocking triggered by suspicious signals, suspected scam calls were diverted into controlled interactions.
This allowed scammer behaviour to be analysed directly.
The intelligence gathered from these interactions revealed patterns that traditional monitoring could not easily detect. Campaign narratives were repeated across operations, infrastructure was reused across campaigns, and activity concentrated within identifiable operating windows.
Operational results included:
- More than 550,000 scam calls diverted and analysed
- Over 450,000 minutes of scam traffic removed from the network
- An estimated 7.6 million dollars in potential financial harm prevented
At the same time, the intelligence captured from scam interactions strengthened existing detection systems by providing deeper insight into how campaigns operate.
Intelligence Is the Next Layer of Telecom Security
Static defences were originally designed to protect network infrastructure. Scam operations behave differently. They function as adaptive businesses that evolve continuously.
Because of this, fraud prevention is shifting toward intelligence-driven visibility.
Networks that can observe scam campaign behaviour gain the ability to move earlier in the lifecycle of an attack. Detection improves, disruption becomes more targeted, and operational precision increases.
Rather than responding to signals once abuse is already visible, telecom networks gain the capability to understand the operation behind the traffic.
This shift introduces a new layer in telecom security infrastructure.
Signal-based controls remain essential. Intelligence adds the missing context required to identify and disrupt the campaigns generating those signals.
Learn how intelligence-led visibility is helping telecom operators expose and disrupt scam campaigns operating across their infrastructure.
Let’s work together.
We work closely with each client to understand their unique requirements and provide a solution that fits. Reach out for a personalised consultation and to explore how our technology can transform your scam prevention and intelligence strategy.

